EIDVirtual
No smart card reader? No problem — turn any USB key into a fully functional virtual smart card.
Download for free
EIDVirtual is free to download. A registration is required after 30 days on Windows Pro and Enterprise editions.
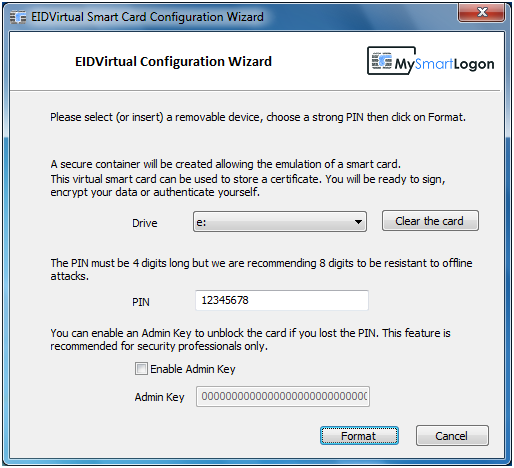
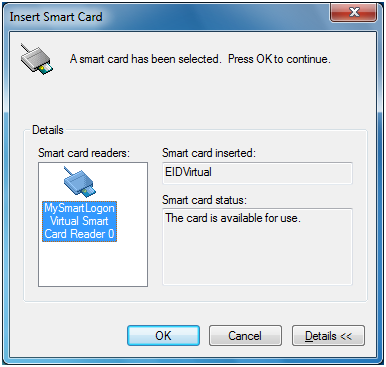
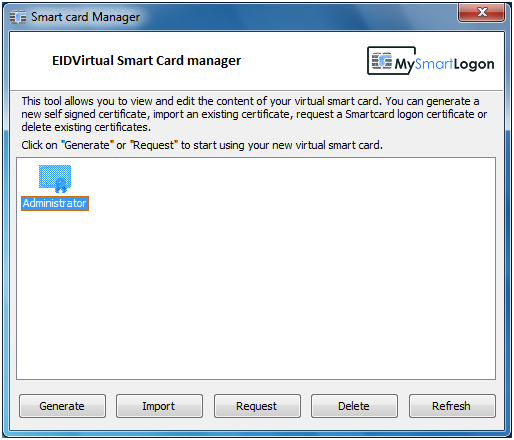
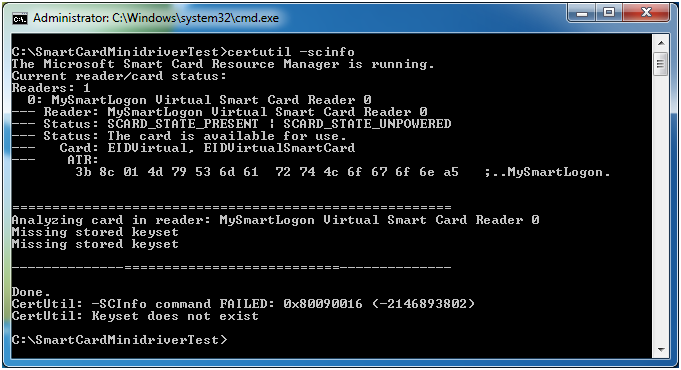
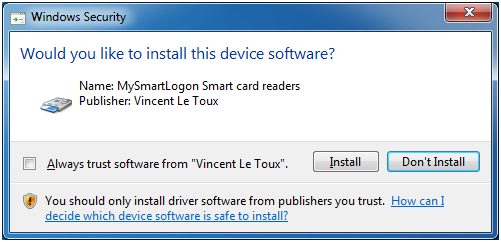
DownloadEIDVirtual makes any USB key appear as a virtual smart card in the Windows device manager. It can then be used for smart card logon via EIDAuthenticate or Active Directory — with no physical smart card reader required.



EIDVirtual was designed for administrators and developers who need to test smart card scenarios, or deploy smart card authentication without procuring physical card readers. The emulation is fully compatible with:
The virtual smart card is also recognized by any remote computer that has EIDVirtual installed, making it fully transparent over Remote Desktop.
- Windows XP / Server 2003 or later
- A USB key or memory card
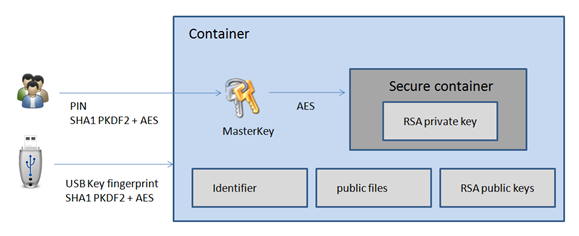
EIDVirtual was carefully designed to protect private keys and PINs. Private data is encrypted twice — first using a USB key fingerprint (including serial number where available, preventing cloning), and second using a PIN-derived key. All cryptographic operations run inside an isolated UMDF host process, separated from all other system processes.