ECC Smart card logon
This procedure sets up ECC (Elliptic Curve Cryptography) for Active Directory smart card logon. You need a read/write smart card that supports one of these ECC curves: prime256v1 / secp256r1, prime384v1 / secp384r1, or prime521v1. The steps below were written using a SmartCard-HSM with the OpenSC minidriver.
Prepare the ECC certificate template
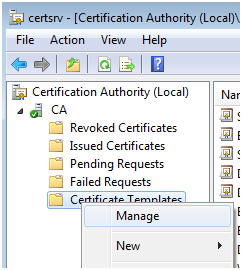
Open the Certification Authority console → right-click Certificate Templates → Manage
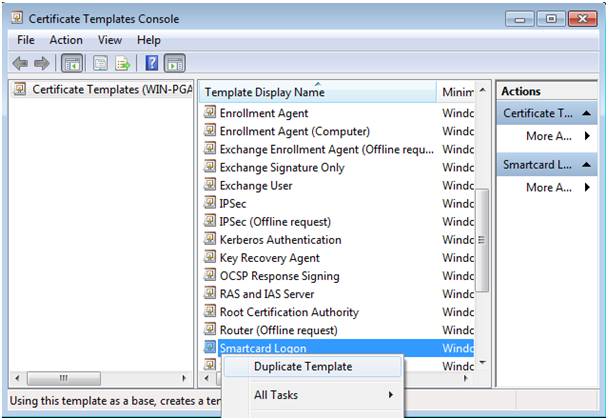
Locate the Smart Card Logon template → right-click → Duplicate Template
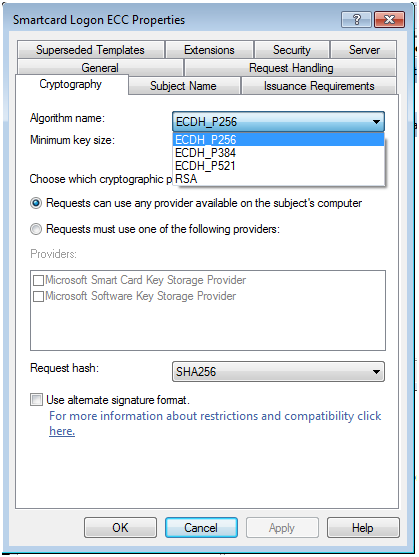
In the General tab, give it a name (e.g. Smartcard Logon ECC). In the Cryptography tab, change the Algorithm name to e.g. ECDG_P256. Optionally change the hash from SHA1 to SHA256.
Deploy the template
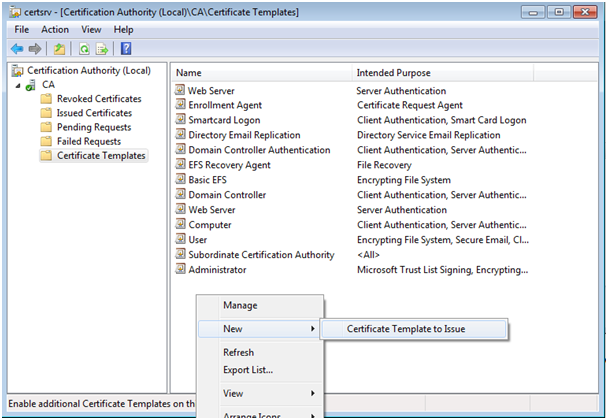
Back in the CA console, right-click Certificate Templates → New → Certificate Template to Issue → select your new template.
Request the ECC certificate
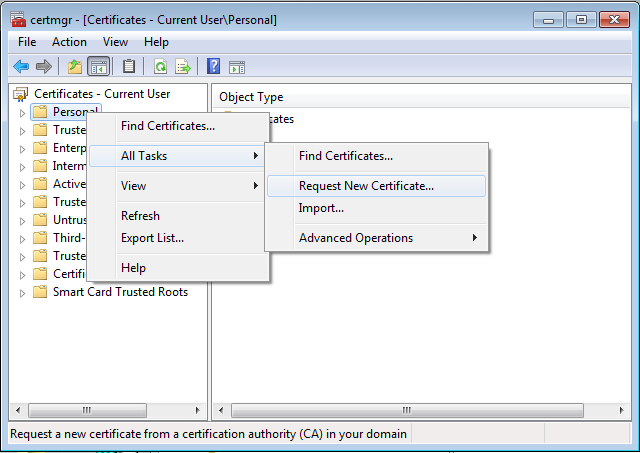
Open certmgr.msc → Personal store → right-click → All Tasks → Request New Certificate
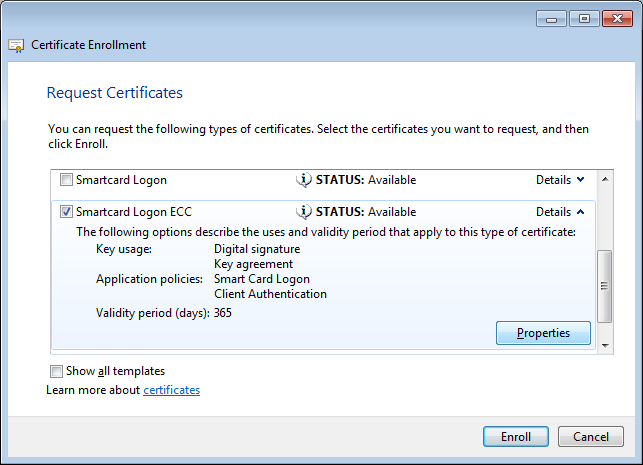
Select Smartcard Logon ECC → click Properties
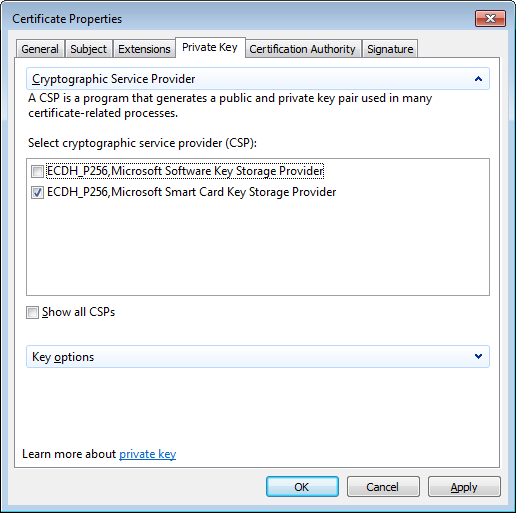
Private Key tab → expand Cryptographic Service Provider → select the KSP associated with your smart card (usually Microsoft Smart Card Key Storage Provider)
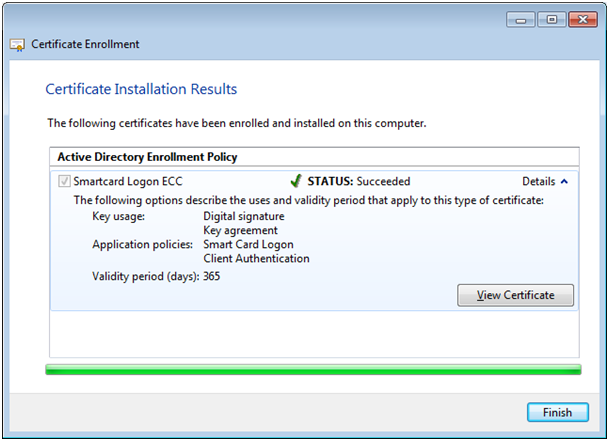
Validate — the certificate will be issued and stored on the card. Verify with certutil -scinfo.
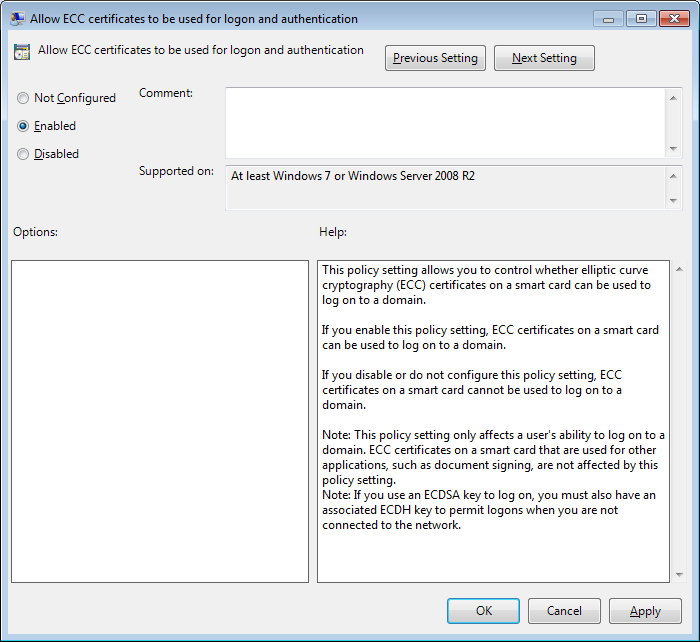
By default, ECC certificates are not shown on the Windows logon screen. Enable the Group Policy setting:
Computer Configuration → Administrative Templates → Windows Components → Smart Card → Allow ECC certificates to be used for logon and authentication
Alternatively, set via registry:
HKLM\SOFTWARE\Policies\Microsoft\Windows\SmartCardCredentialProvider "EnumerateECCCerts"=dword:00000001
