CNG calls for ECC smart card logon
lsass.exe / kerberos.dll
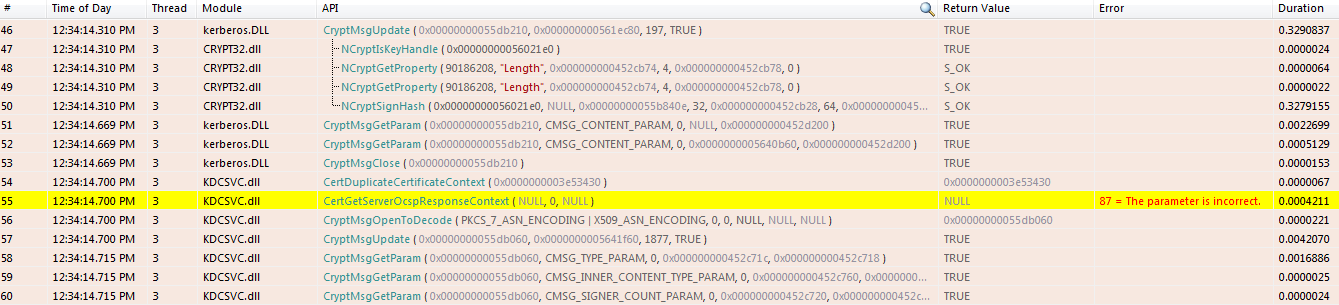
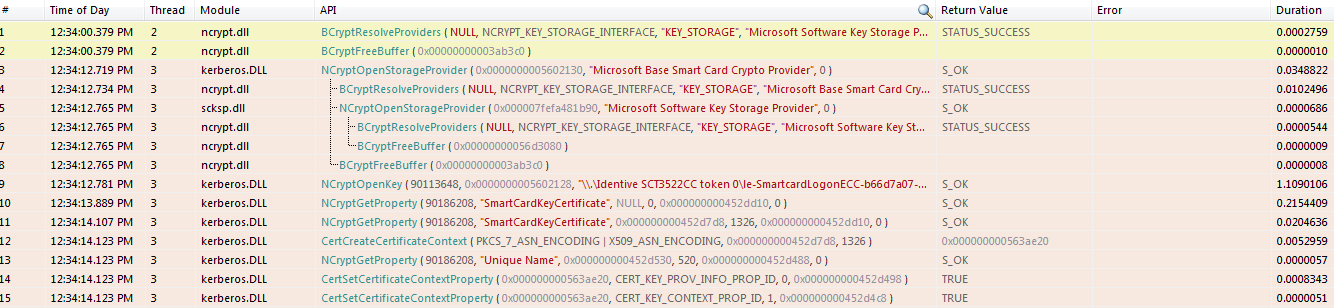
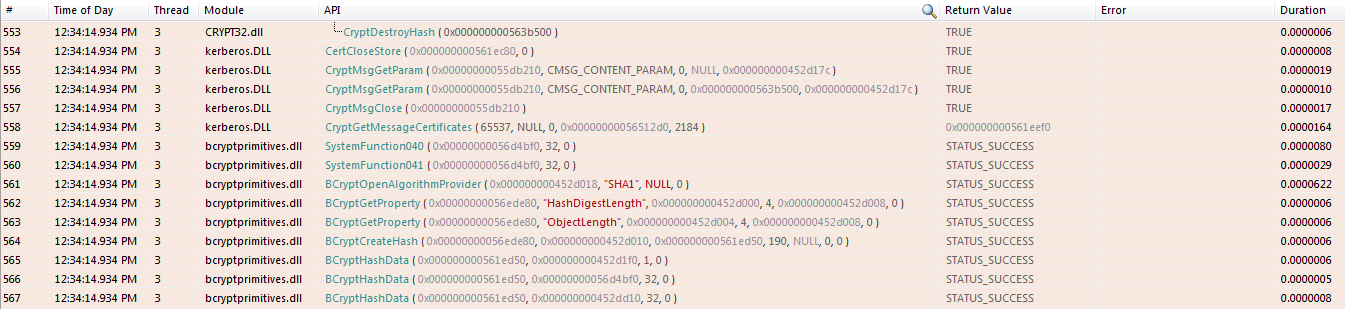
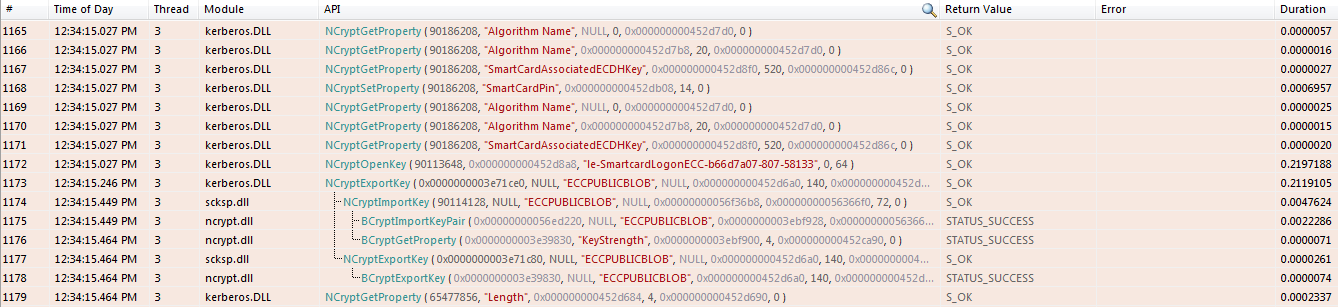
The following sequence is executed during ECC smart card logon. Each step corresponds to a CNG/CryptoAPI call observed via reverse engineering.
NCryptOpenKey + GetProperty (certificate)
NCryptOpenKey(handle, "\\.\reader\containername", 0, 96);
NCryptGetProperty(handle, "SmartCardKeyCertificate", NULL, 0, &size, 0);
NCryptGetProperty(handle, "SmartCardKeyCertificate", buffer, size, 0);
CertCreateCertificateContext(PKCS_7|X509, buffer, size);
NCryptGetProperty(handle, "Unique Name", buffer, 520, &size, 0);
CertSetCertificateContextProperty(handle, CERT_KEY_PROV_INFO_PROP_ID, 0, handle);
CertSetCertificateContextProperty(handle, CERT_KEY_CONTEXT_PROP_ID, 1, handle);
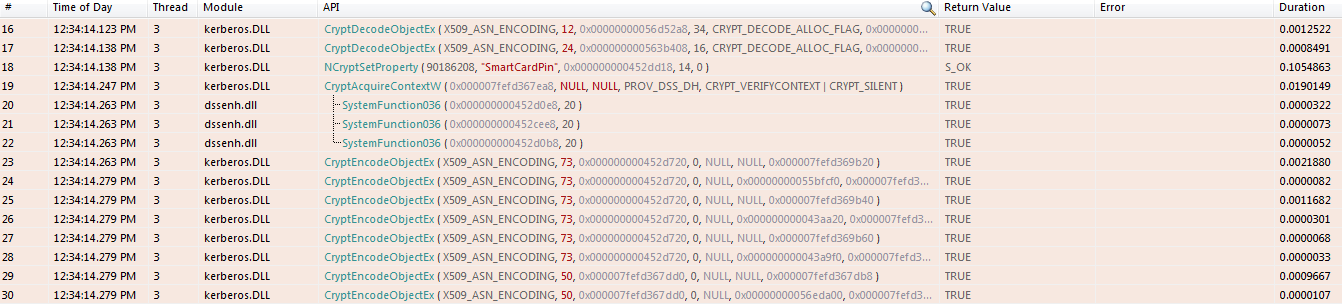
NCryptSetProperty (PIN) + random generation
NCryptSetProperty(handle, "SmartCardPin", pbBin, (pin_length+1)*2, 0);
CryptAcquireContext(&handle, NULL, NULL, PROV_DSS_DH, CRYPT_VERIFYCONTEXT | CRYPT_SILENT);
BCryptGenRandom(32 bytes, BCRYPT_USE_SYSTEM_PREFERRED_RNG);
BCryptGenRandom(40 bytes, BCRYPT_USE_SYSTEM_PREFERRED_RNG);
CryptMsgOpenToEncode(CMSG_SIGNED, 1.3.6.1.5.2.3.1);
CryptMsgUpdate(); CryptMsgClose();