Save a pfx/p12 file to a smart card
Step 1 — Identify the smart card name
Open a command prompt and run:
certutil -scinfo
Look for the Card line in the output:
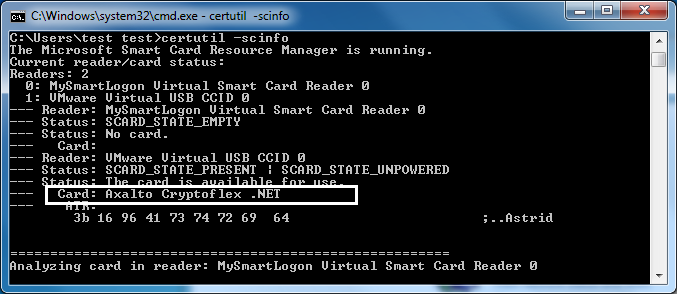
certutil -scinfo outputReaders : 1 0: FS USB Token 0 --- Reader : FS USB Token 0 --- Status : SCARD_STATE_PRESENT | SCARD_STATE_UNPOWERED --- Status : Card available. --- Card : ePass2003 --- ATR : 3b 9f 95 81 31 fe 9f 00 66 46 53 05 01 00 11 71 df 00 00 00 00 00 13
In this example, the card name is ePass2003. If the card already contains cryptographic material, a Provider line is also shown — you can then skip step 2.
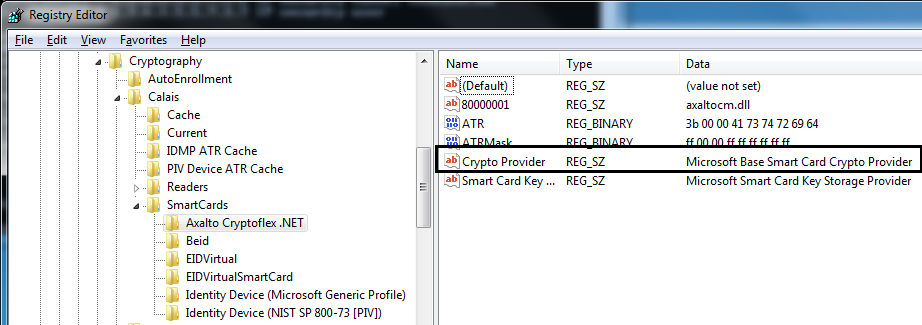
Step 2 — Find the CSP name in the registry
Open regedit.exe and navigate to:
HKEY_LOCAL_MACHINE\Software\Microsoft\Cryptography\Calais\SmartCards\{card name}
Look for the Crypto Provider value — this is the CSP name you will use in step 4.
Step 3 — If using "Microsoft Base Smart Card Crypto Provider"
By default, importing a P12 file is blocked when the CSP is Microsoft Base Smart Card Crypto Provider. The import fails in
CryptImportKey with error NTE_BAD_TYPE (0x8009000A).
Set the following registry values to allow import:
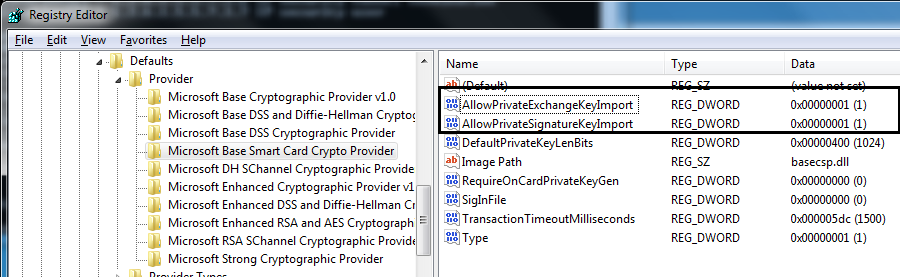
Or apply this .reg file:
Windows Registry Editor Version 5.00 [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\Defaults\Provider\Microsoft Base Smart Card Crypto Provider] "AllowPrivateSignatureKeyImport"=dword:00000001 "AllowPrivateExchangeKeyImport"=dword:00000001
Step 4 — Import the PFX
certutil -csp "{CSP name}" -importpfx {PFXfile}
Example:
certutil -csp "Microsoft Base Smart Card Crypto Provider" -importpfx foo.pfx
